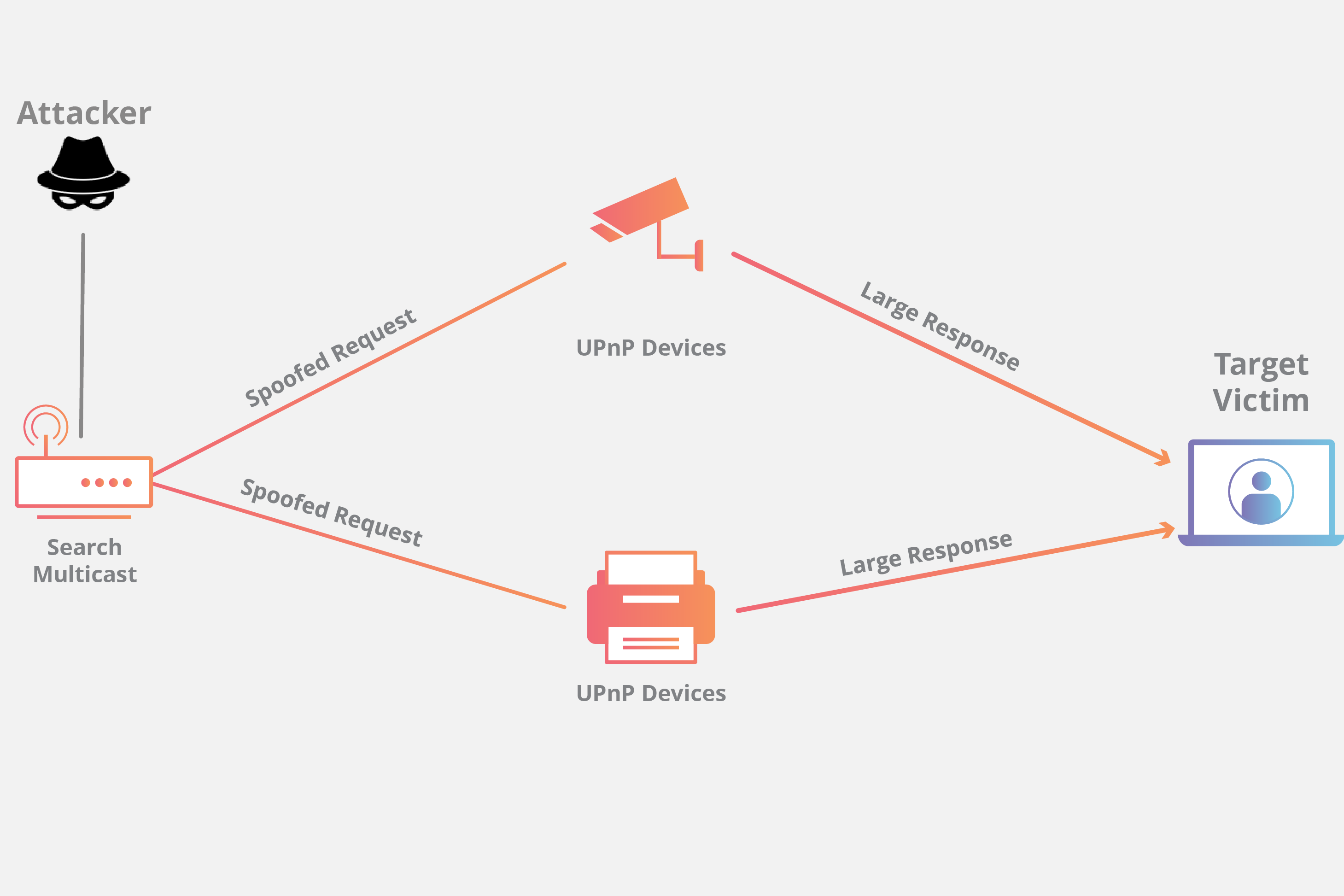
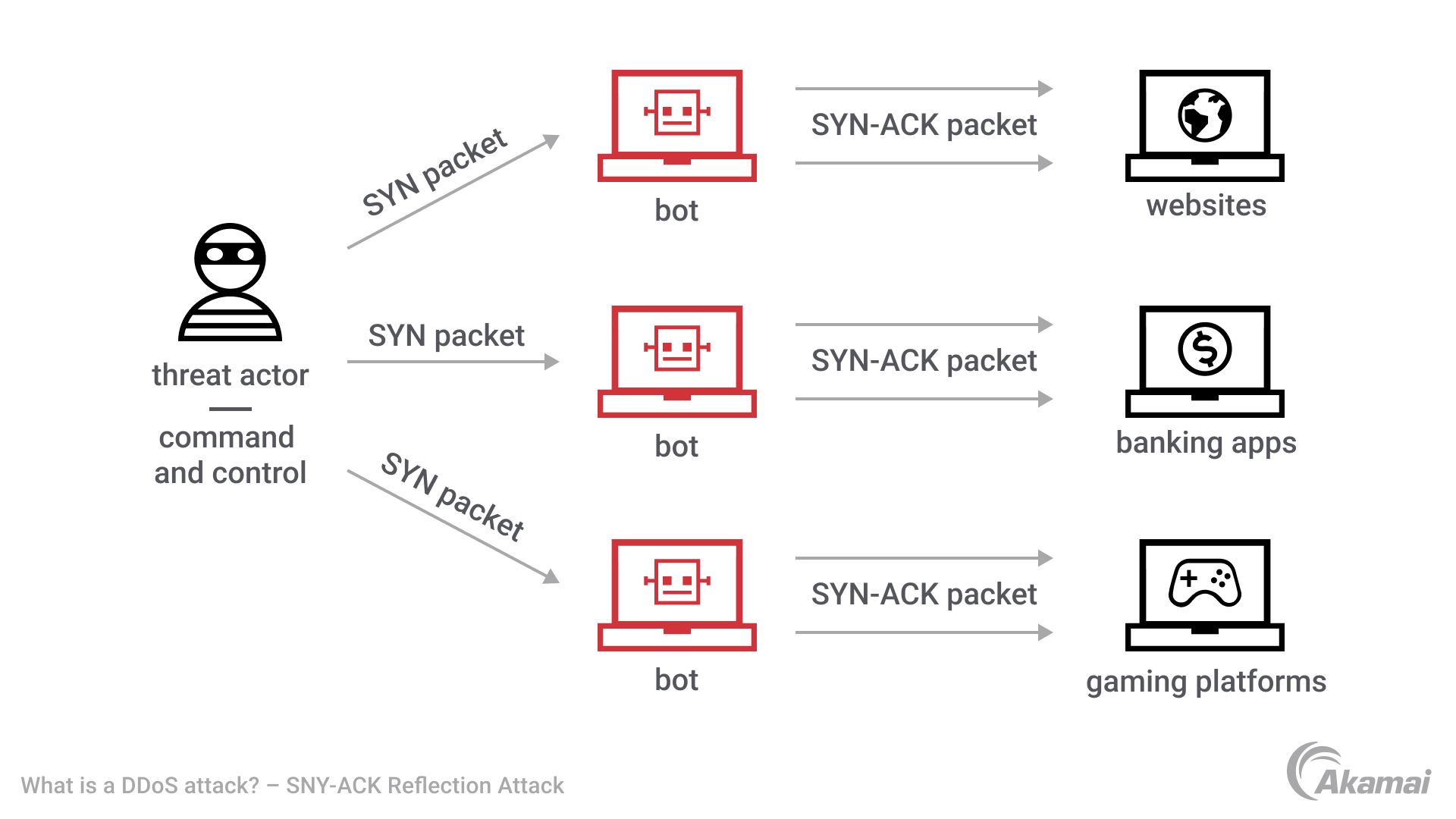
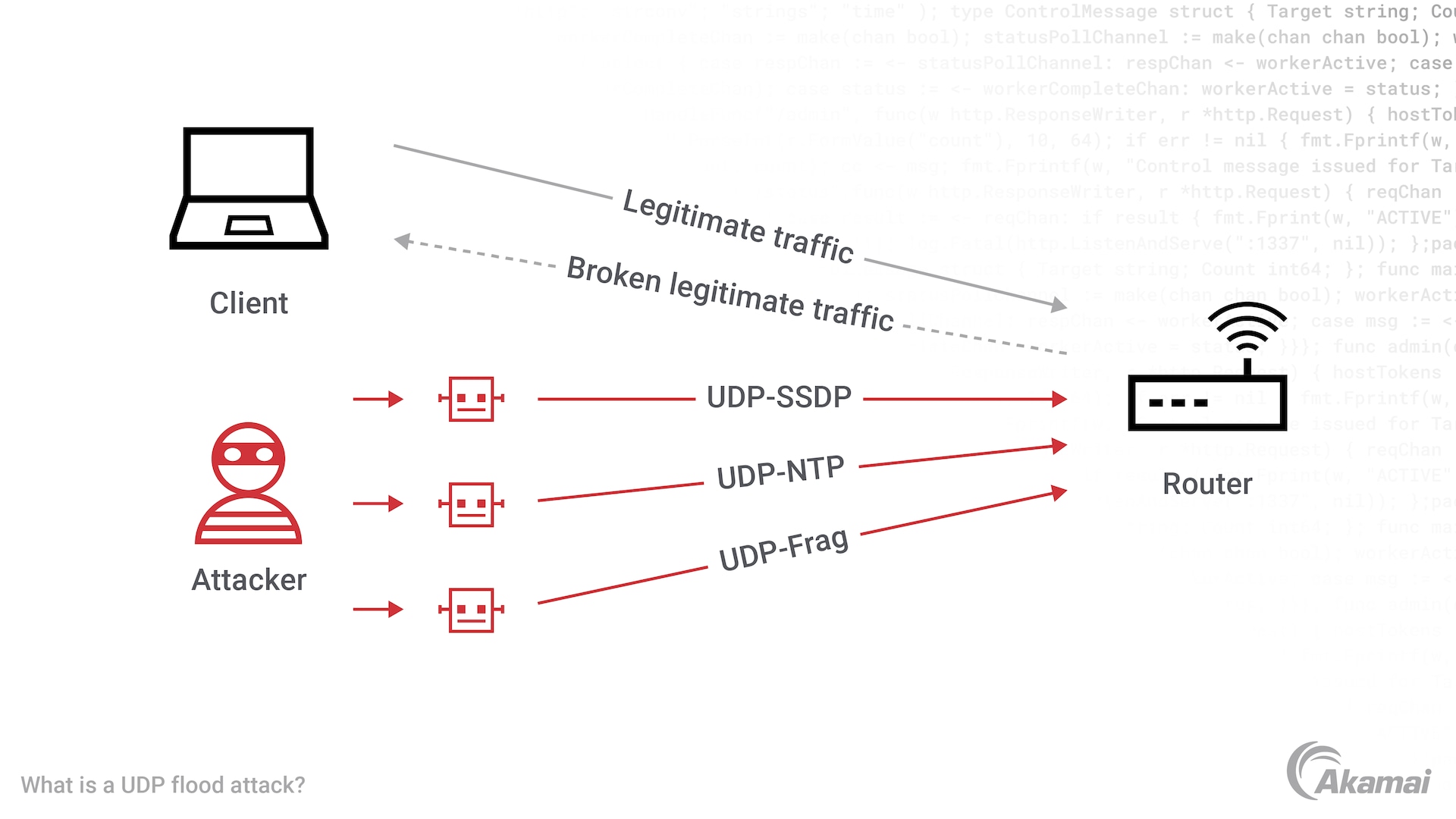
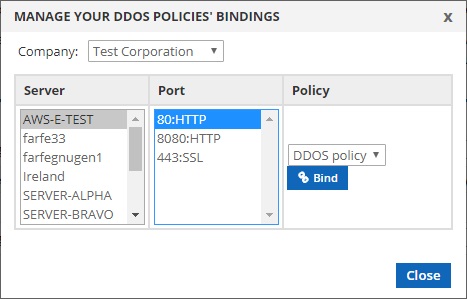
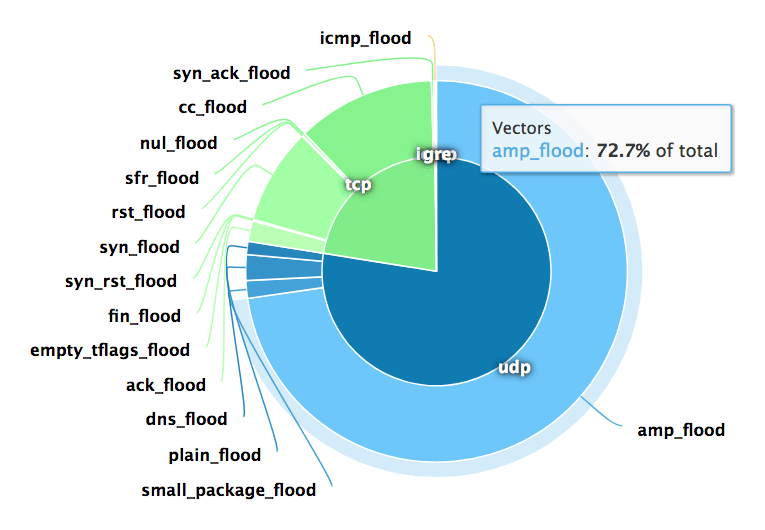
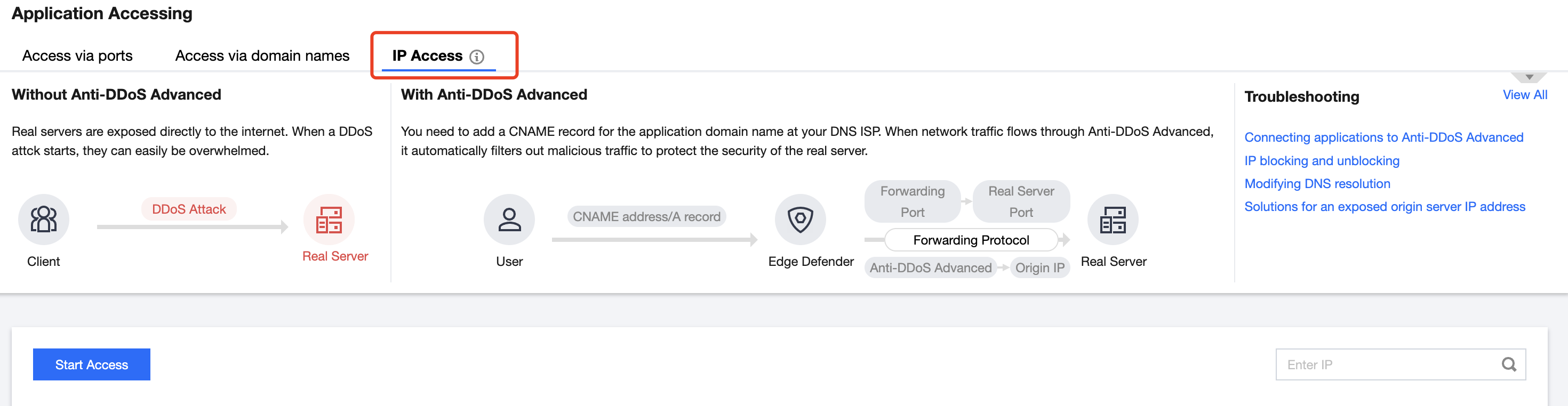
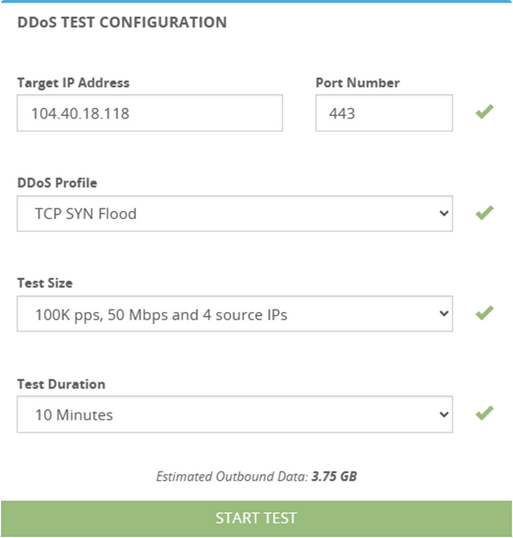
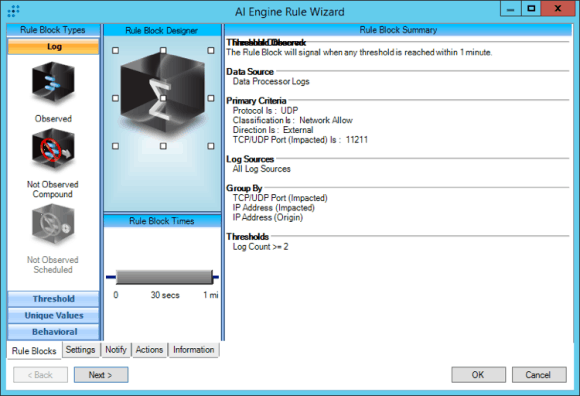
Applied Sciences | Free Full-Text | A Secure and Intelligent Software-Defined Networking Framework for Future Smart Cities to Prevent DDoS Attack
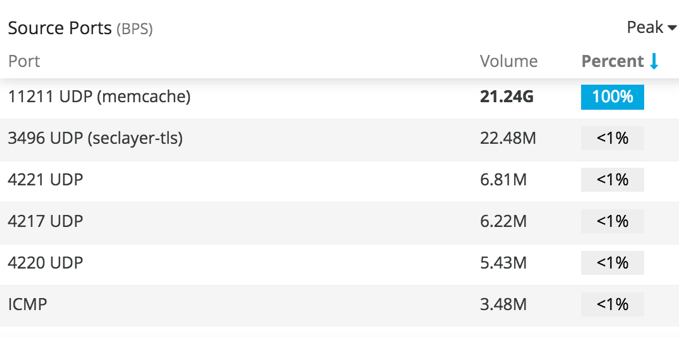
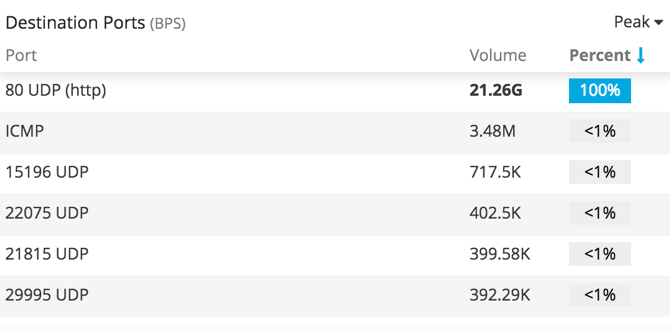
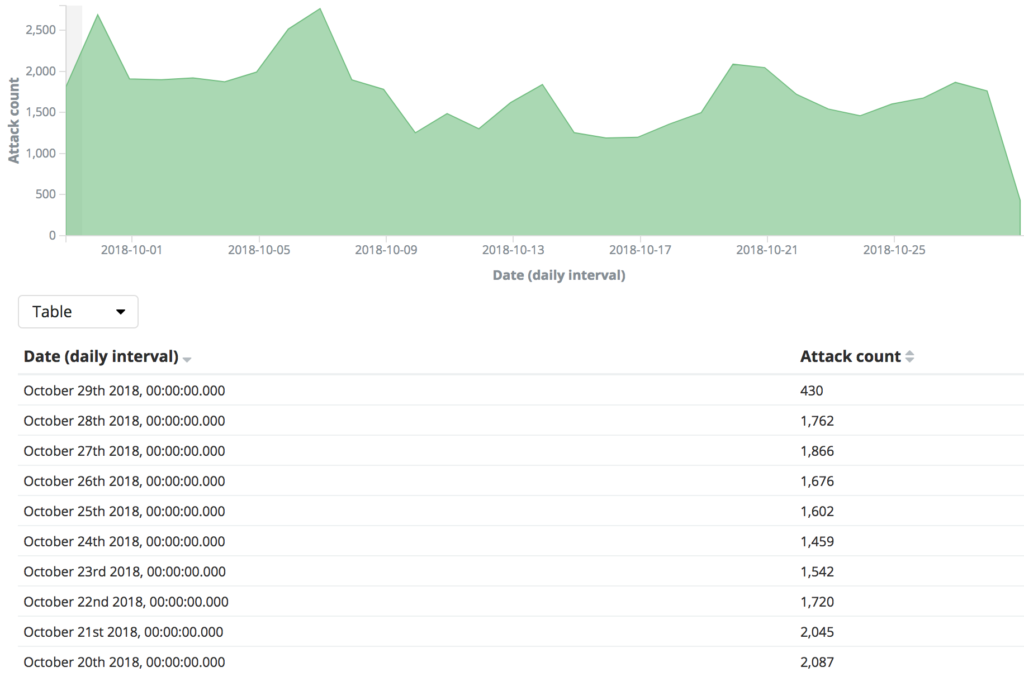
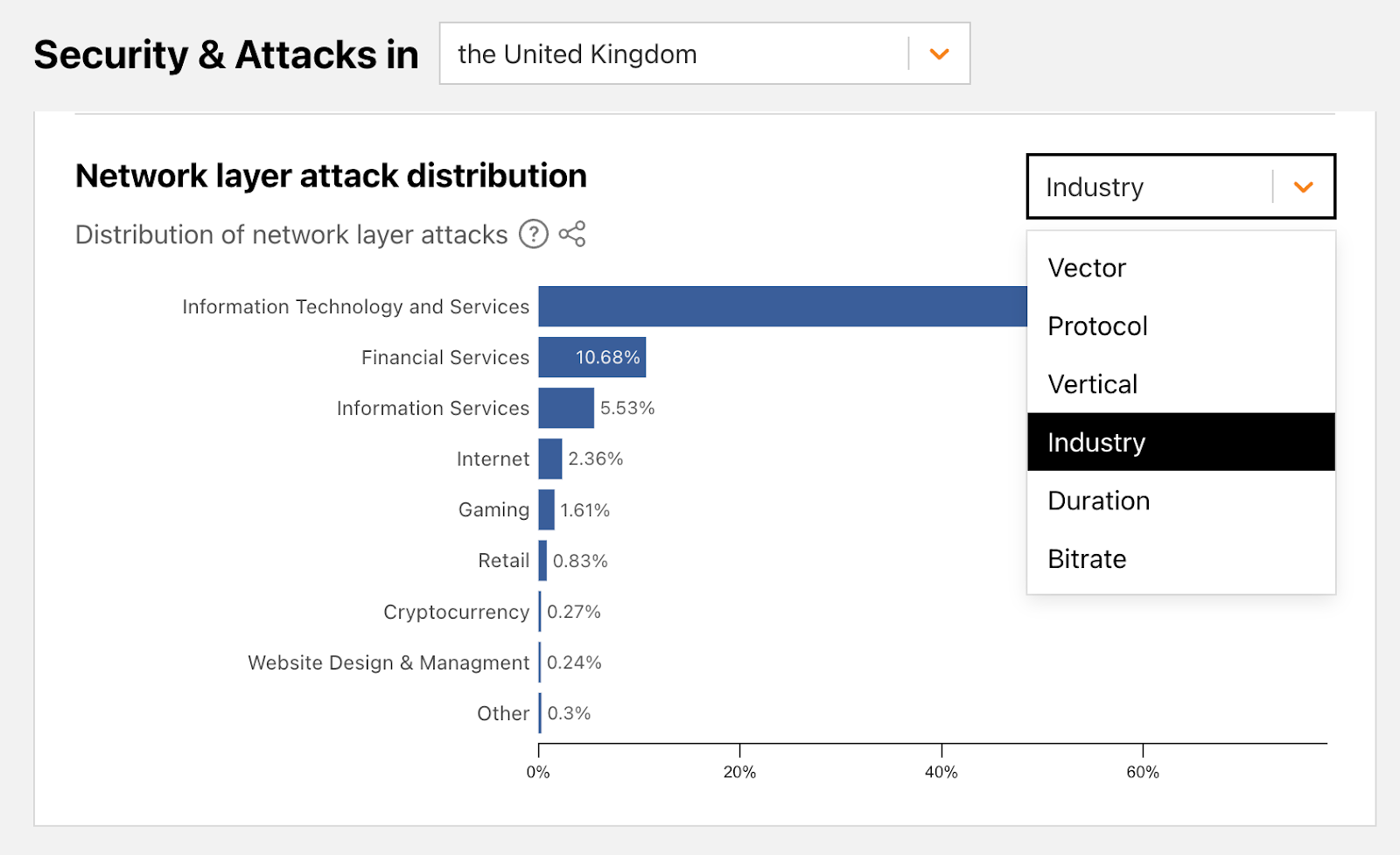
Enhanced Infrastructure DDoS Protection Analytics: Targeted Visibility for Greater Accuracy | Imperva
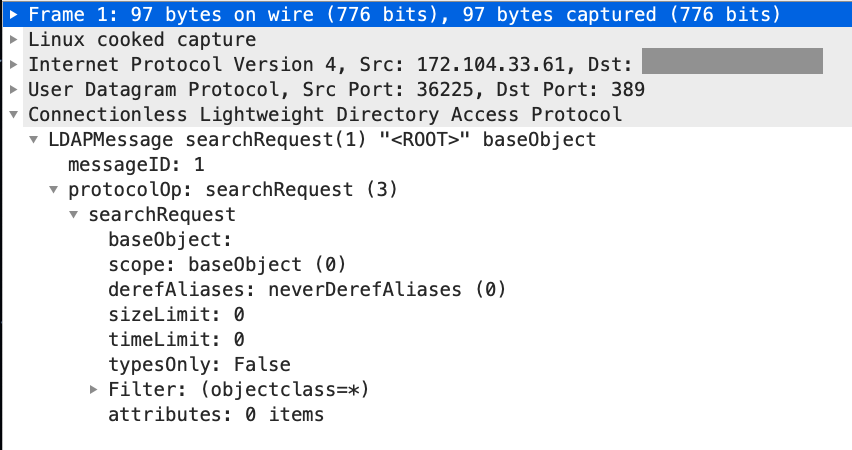
Denial of Service (DoS) attack identification and analyse using sniffing technique in the network environment